The start of this process by a non-human account is another great detection opportunity. In addition, on one host, the average LSASS interaction, with access right 0x1FFFFF by the explorer process was ~13K every two hours. Inspecting memory dumped from the host, the injected processes were easy to discover using Volatility and the malfind module. Looking for output that included explorer.exe and contains the VAD tag PAGE_EXECUTE_READWRITE and MZ headers in the memory space, common attributes observed for process injection in memory. Upon execution of the MSDT payload, a new instance of the sdiagnhost.exe was spawned. This process was ultimately responsible for invoking the Follina payload, starting, in our case, three child instances of regsrv32.exe .
- Although ImageMagick runs well on a single core computer, it automagically runs in parallel on multi-core systems reducing run times considerably.
- If the selected VPN Gate Server supports both TCP and UDP protocols, the above screen will appear.
- S0660 Clambling Clambling can store a file named mpsvc.dll, which opens a malicious mpsvc.mui file, in the same folder as the legitimate Microsoft executable MsMpEng.exe to gain execution.
- I will show you a nice tool called dnspy that allows you to open and explore a DLL or EXE file.
A window will pop up asking, «Do you want to run this process?». If your antivirus have not helped you solve the problem, you should try UnHackMe. Download Outbyte PC Repair to solve dozens of system issues and fix corrupted elements.
DLL is short for Dynamic Link Library, and it is a type of file which comprises a set of instructions used by other programs to accomplish certain functions. Many of them were developed by companies such as Microsoft or Adobe and are assigned to run specific programs. DLL files are designed to be called by several apps at once.
Standalone Version
In runtime dynamic linking, you use code that is similar to the following code to call the SampleDLL.dll exported DLL function. When you create a DLL, you can optionally specify an entry point function. The entry point function is called when processes or threads attach themselves to the DLL or detach themselves from the DLL. You can use the entry point function to initialize or destroy data structures as required by the DLL. The GUMU™ Cloud framework by Greytrix forms the backbone of cloud integrations that are managed in real-time for processing and execution of application programs at the click of a button.
As you see it should hold another XML container which is called iYield, so we need to tell the XML what to expect in iYield as well. Then we use a «p» to state that we are using an array, and as before, an «i» to indicate that we are using integers, or a «b» download api-ms-win-downlevel-kernel32-l2-1-0_dll link to indicate booleans. First, we set the variable bFound to FALSE to act as a flagging variable (as just discussed, so we can add a comma or realize that we didn’t find any Unique Units at all). First spot we come to is adding to the Civilization Information. This will cover both the Dawn of Man screen at the start of a new game AND the Civilizations section of the Civilopedia, which naturally covers the PLAY NOW screen for us as well. Remember during this test also that nothing should be any different than it was before adding your new tag right now.
Use by malware
Decompiler is the safe option as with Decompiler, you can look at the code without changing it, and it won’t affect your system. I think you need to decompile a .dll to change or look at any info. If you check the /mods/help forum on ludeon.com you should find a list of all the programs people use for modding Rimworld. DLL files are not developed with the intention of opening by the users.
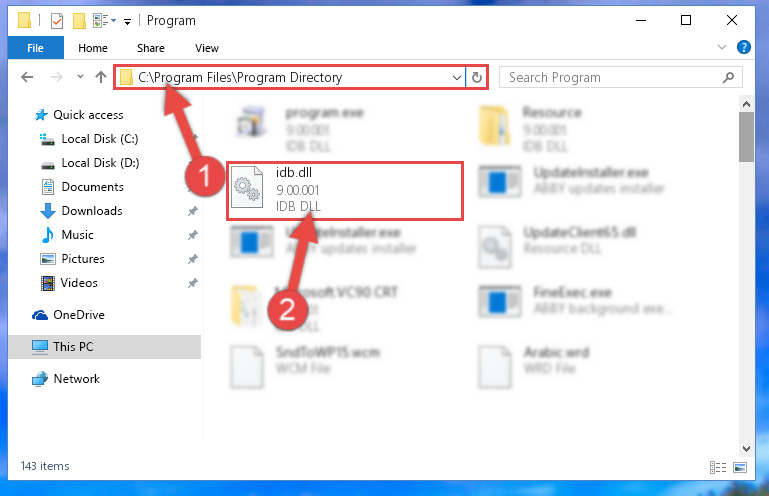
How to install DLL files in Windows 10?
After the command prompt loaded to the screen, type ILDASM.EXE press ENTER. Yes, but making changes is risky because because these are compiled files. If you want to change code, first backup your original files, then you can use the «Resource Editor» to edit and save the DLL.
